The certificates management is related to the server name and the services provided (please refer to PSAM 2.2 Network Segregation for details about the certificate assignation to a specific NIC/IP/name). In order to provide to the client a sure match of your identity you need to load and configure a secure certificate bonded to your server name (ie: name.server.tld).
|
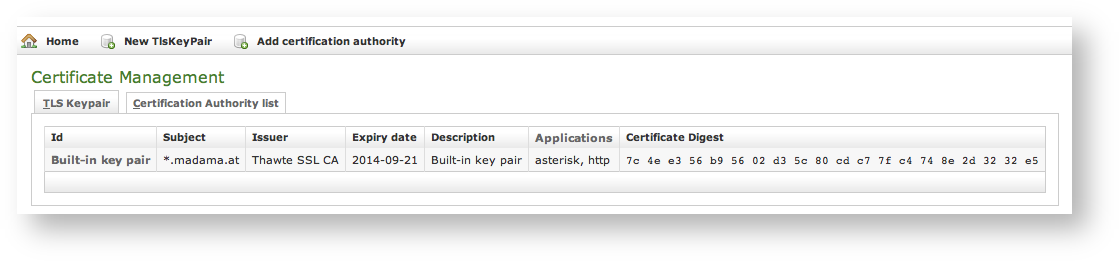
You can get the certificates configuration page using the Certificate Management link in the main menu. As shown above the default page is listing the installed TLS Keypair.
By default, on PrivateServer it's installed one "*.madama.at" wildcard certificate as shown in |
|
From this page you can decide to view and delete your keypairs or the Certification Authority entries, using the tabs shown in the above .
|
Instead if you need to create a new TLS key pair or add a new CA, then you have to use the buttons above the "TLS Keypair" list (the ones shown in ).
If you need to upload a new certificate, click on the New TlsKeyPair link above the certificate table.
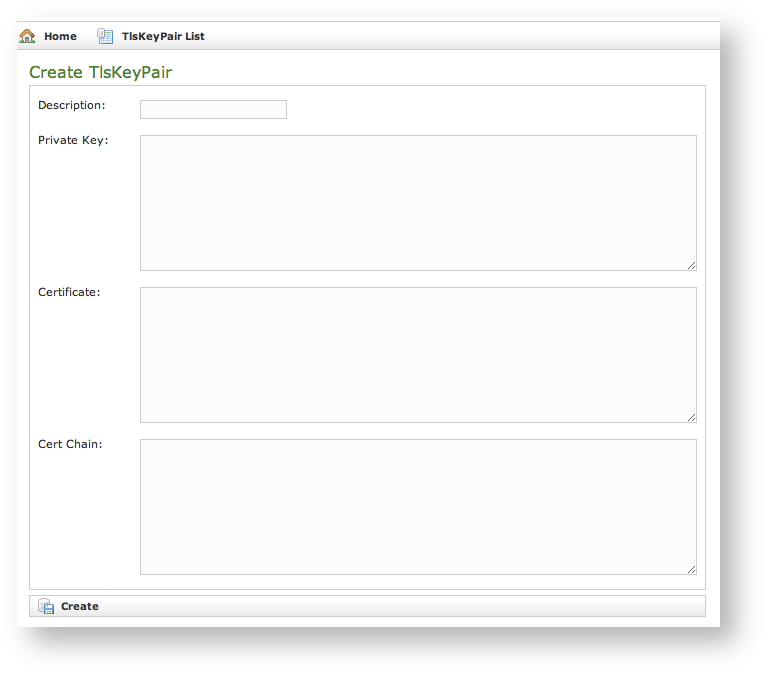 |
You are redirected on the Create TlsKeyPair page (it's shown in ) where an upload form needs to be filled. Its fields are:
All the fields must be in PEM (Privacy Enhanced Mail) format and you just copy and paste each of them in the proper field. When your' done you just press the Create button on the bottom line and the certificates are ready to be assigned to an interface/IP.
You might need to upload a new CA (Certification Authority) if you tried to install a tis key pair not signed by an installed CA.
By default PrivateServer contains a default list of pre-loaded Certification Authorities. |
|
The new CA installation becomes mandatory because without a complete certificate chain the new TLS key pair would not be accepted by PrivateServer. If you need to upload a new certificate, click on the Add certification authority button above the certificate list table.
|
You get the form shown in which is pretty straightforward. You just have to cut 'n' paste the CA's content in the Certificate box and click on the Create button at the bottom.
|
As shown in the Certification Authority list shows a new entry. You can check the entry by subject (which is the entity that release the certificate) and the expiry Date (that shows how long the certificate is considered valid).
In a day-by-day secure VoIP service administration it's not unusual to delete a TLS key pair. The procedure starts right at the Certificate Management page (the one shown in .
|
In you can see we added an entry conveniently named testing entry to be deleted and that's what we're going to do.
Please make sure no services got association with the TLS entry you're going to remove, or else the deletion would fail. |
|
First you click on the chosen entry and get a detail of the TLS key pair (as in ). At the page's bottom there's a Delete button. Just press it.
|
Confirm the deletion in the following pop-up windows. After that you get the new TLS key pair list without the deleted entry and with a warning which explains the entry has been deleted (as in ).
You cannot edit an entry in the CA list, but you still can delete a CA and create a new one for replacement. That said, the way for deleting a CA entry is quite simple. From the CA list shown in choose the CA you want to expunge and press the Delete link in the last right column.
|
First you get a detail of the certificate you're going to delete. Just press the Delete button at the bottom and confirm your choice in the next pop up window.
|
You receive a confirmation about the deletion in the new CA list page (shown above in ). Plus the list no more shows the deleted CA entry.