Secret Security applies an End-To-Site security model, where audio data is encrypted on one call-end and decrypted on PBX side. This model, used within Enterprise VoIP Security Suite, uses the same paradigm of VPN: the call is secured outside of the company network and goes in clear inside the company network. The main advantages of End-To-Site security model are:
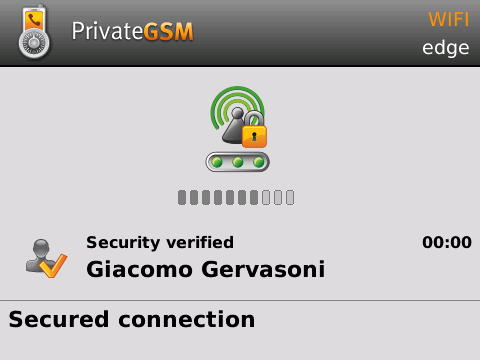
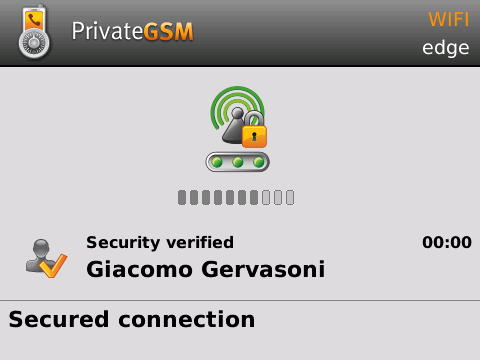
Call is automatically secured during call setup so it does not require any human intervention. As soon as call is established you can immediately start to talk with securely your peer. The overall security verification system is based on TLS digital certificate verification. The PrivateGSM Enterprise client automatically verifies the digital certificate of the SIP/TLS server and if it's recognized and authentic, the connection will be automatically secured.
 |
 |
This security model is exactly the same as HTTPS with internet browser, given the fact that on PrivateServer there is a valid digital certificate the call can be considered secure. By default, PrivateGSM will not accept invalid SSL certificates, such as:
If the SSL certificate is a wrong or invalid (ex: one of the above mentioned reasons) or in the case of a man in the middle attack attempt, the user will see the following warning on the phone display:
| SSL error message |
|---|
You are attempting to open a secure connection, but the server's certificate is not trusted. Please contact your system administrator |
On BlackBerry phone the message may be different, because it is a warning message of the operating system. It may also change in every operating system release.
Since security is based on TLS digital certificates, it is mandatory that server certificates are signed by a known and trusted certificate authority. If your certificates is signed by a new CA (not present in phone CA list at ship time) or your private CA, you can import the CA's certificate and trust it. This feature is available only for OEM version of PrivateGSM.